We all know that there is no pure Microsoft environment. There is for example often a old Linux box, and that box need to be monitored as well as everything else. If you answer “no, it dont”, why dont you shut down that box immediate? In this post I will show how to get syslog messages from a Linux machine (Red Hat Fedora 6) into your Operations Manager 2007.
First you will have to modify your Linux to forward messages to your Operations Manager machine, and then create a rule in your Operations Manager server.
You will have to modify your Linux to forward messages to your Operations Manager machine. That you will do in the /etc/syslog.conf file. At this screendump you can see that I have added one line that will send all messages (*.*) to my Operations Manager server (10.1.3.15). After added that line, and save changes (:wq!), you will have to restart the syslog service, that you can do with “service syslog restart”. There are a lot of settings that you can do in the syslog.conf to only forward some category of messages.
After that the Linux side is finish. As you can see with the “netstat –an†your Operations Manager server is not listening to the standard port (UDP port 514) by default. Your server will not do that until you have an active rule (not disabled) that use SysLogDS as data source. To create a rule to collect your syslog messages,
- From the Start Menu, select the SCOM Operations Console
- In the Navigation pane (left), Click Authoring
- In the Authoring pane, right click Rules and choose “Create a new rule…†from the context menu
- On the Select a Rule Type screen, select Alert Generating Rules\Event Based\Syslog (Alert), click Next
- On the General screen, input a suitable rule name and a description, click select and choose your management server in the select a target type window (select the machine that will recive syslog messages), click OK, back on the General screen, click Next
- On the Build Event Expression screen, create an expression, unfortunately I have not figur how to build a good expression. Input a expression and then delete it later. Click Next
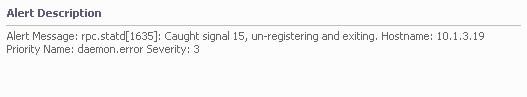
- On the Configure Alerts screen, input an alert name, priority and severity. In the Alert description box, input as this screenshot. If you dont do this there will be no alert description in the console. With this config you will get a alert description like below. Click Create.
- In the Rules pane, right click your new rule and choose “Properties†from the context menu
- On the rule properties screen, click the Configuration tab
- On the rule properties screen and the configuration tab, click Edit under Data Sources
- On the expression screen, select the expression and click Delete. Click OK
- On the rule properties screen, click OK
That should do it!
Now we dont have a filter on the Ops Mgr side, but you can filter on the Linux/syslog side, until you have figur out how to do a good filter on the rule. You read about creating filter in this KB from Microsoft. It is about syslog in MOM 2000/2005 but the filter part is the same.
Â
Â
 DPM MP Reports
DPM MP Reports
[…] Creating Linux Syslog Monitor […]
[…] Rather than re-document some of the excellent blog posts around (see http://contoso.se/blog/?p=158 for some excellent background), I simply wanted to cover some of what isn’t known:- […]
[…] Syslog is used extensively by *Nix machines. There is a good post from Anders about using syslog and a step by step guide to creating an example – http://contoso.se/blog/?p=158. […]